What is P-SSCRM?
14 Oct 2025 -
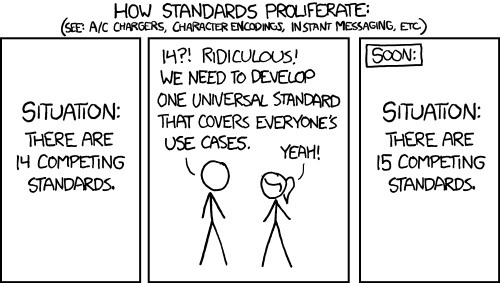
One thing the Proactive Software Supply Chain Risk Managementi (P-SSCRM) framework is not is another standard. Rather than introducing any new concepts, practices, or tasks, we have aggregated concepts, practices, and tasks from existing software supply chain security frameworks.
P-SSCRM is designed to help you understand and plan a secure software supply chain risk management initiative. P-SSCRM was created through a process of understanding and analyzing real world data from nine industry leading software supply chain risk management initiatives as well as through the analysis and unification of ten government and industry documents, frameworks, and standards. Although individual methodologies and standards differ, many initiatives and standards share common ground. P-SSCRM describes this common ground and presents a model for understanding, quantifying, and developing a secure software supply chain risk management program and determining where your organization's existing efforts stand when contrasted with other real world software supply chain risk management initiatives.
| Practice | P-SSCRM | 800-161 | BSIMM | CNCF-SSC | EO | OSSF-Scorecard | OWASP-SCVS | SLSA | SSDF | SSDF-AI | Self-attestation |
|---|---|---|---|---|---|---|---|---|---|---|---|
| G.1 Perform compliance | |||||||||||
| G.2 Develop security policies | |||||||||||
| G.3 Manage suppliers | |||||||||||
| G.4 Training | |||||||||||
| G.5 Assess and manage risk | |||||||||||
| P.1 Develop security requirements | |||||||||||
| P.2 Build security in | |||||||||||
| P.3 Manage component and container choices | |||||||||||
| P.4 Discover vulnerabilities | |||||||||||
| P.5 Manage vulnerable components and containers | |||||||||||
| E.1 Safeguard artifact integrity | |||||||||||
| E.2 Safeguard build integrity | |||||||||||
| E.3 Secure software development environment | |||||||||||
| D.1 Respond to/disclose vulnerabilities | |||||||||||
| D.2 Monitor intrusions/violations | |||||||||||
| U.1 Identify SSC Control Gaps | </tr> |